Concept is simple: Veeam B&R uses StarWind Virtual Tape Library (VTL) to store backup files as emulated tapes in local cache and then VTL replicates these tapes to Amazon S3/Glacier. Amazon S3 Standard - Infrequent Access for long-lived, but less frequently accessed data, and Amazon Glacier for long-term archive.
The main StarWind advantage is performance; It writes backup files to local cache ten times faster than native Amazon VTL.
Let have a quick look on how the product in action...
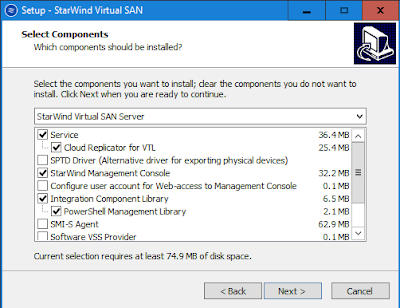
To start, you can download Starwind Cloud VTL for AWS from here. Install the VTL on any VM/Veeam Backup Server.
Configure Starwind VTL:-
- Add VTL Device
- Specify the VTL store location
- Select Device to Emulate. It will emulate HP MSL8096
- Create new tape or fill up the empty tape.
- You can only specify LTO 4 or LTO 5 (max size 1.5TB per tape)
Get AWS Account. For testing, you can sign up for Free Tier (up to a year) from https://aws.amazon.com/free/
- Create a user (example:- vtladmin)
- Get an access key and secret access key
- Assign user to a group - AmazonS3FullAccess and AmazonGlacierFullAccess
Create S3 bucket. Point to region that you want.
I've selected Asia Pacific (Singapore).
Configure Starwind VTL
Next step is configure Cloud Replication.
- Define Access Key ID (refer to setting that you've on above step)
- Define Secret Access Key
- Define Region
- Define Bucket
Note:- Asia Pacific Region does not transition data from S3 to Glacier. Select other region if you want to tier to Glasier.
Specify your tape file retention settings:-
A. When start replication to cloud when tape moved from drive.
-can be immediate
-never replicate (offline)
- set days
B. Acton after data has replicated to cloud for local copy
- delete immediately
- never delete (local copy available)
- set days
C. Action when move to Glacier
- Enter iscsi target where you've installed Starwind VTL
Download latest driver from https://h20566.www2.hpe.com/hpsc/swd/public/detail?swItemId=MTX_7e9f343865d1445e92cfbaf0b1
On Veeam Backup Server
- Perform rescan tape libraries
- New tape library has added "HP MSL G3 Series 1070" with up to 4 drives & 96 tape available.
- Make Tape as free
- Create Simple Media Pool or GFS media pool (depend on your requirement)
Testing by create File to Tape Job
- Tick Use Microsoft VSS
- Eject media upon completion
- Eject Export current media upon job completion
- Run backup
You can view tape backup status
After backup complete, tape will automatically moved to Media "Offline". You can view the content that you've backup previously.
On Starwind Management Console:-
- Tape has moved to Offline Shelf
- Tape indicated Local - None, Cloud - Yes. Mean local copy has removed and replicated to Cloud
On S3 bucket, able to view VTL tape that has successful replicated.
Testing restore by getting tape from AWS S3
- On Offline Shelf, click the tape & select download.
- Tape status - Local -Yes, Cloud - Yes . (mean has downloaded and able on local)
- Tapes listed on Tapes
On Veeam B & R, inventory the tape. It will loaded into one of emulated drives.
Lastly, Restore. You can see your content and perform any recovery from the tape.
- Implementation of Disk-to-Disk-to-Cloud (D2D2C) backup strategy
- Veeam Ready solution
- Ability to “tier” backups between cloud storage with different performance and efficiency characteristics for maintaining low cost per GB without compromising RTO.
Give it a try. The product is now available for use. You can get Starwind VTL trial license and evaluate for 30 days.
Good Luck on your testing!