Hi reader, do you have an existing Vmware Virtual Machine and would like to move it to Azure?
If yes, please read further on how we use MVMC 3.0 to perform migration from Vmware to Microsoft Azure.
[Requirement on Vmware]
- Vmware vSphere 5.5, 5.1 and 4.1
- Vcenter 5.5,5.1 and 4.1
[ Supported guest operating system on Microsoft Azure]
- Windows Server 2012 R2
- Windows Server 2012
- Windows Server 2008 R2
- Ubuntu 12.04
- Suse Linux Ent 11
- Centos 5, 6
- Debian 7
- Oracle Linux 5, 6
[ Microsoft Azure]
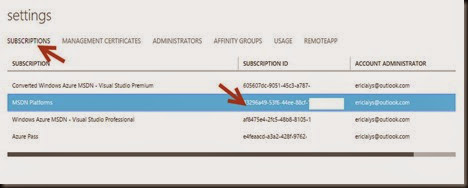
Get an Azure subscription
- identify Azure Subscription ID
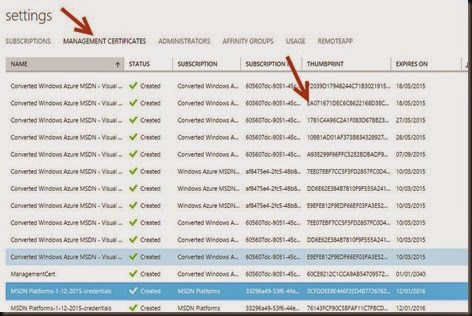
- identify management certificate thumbprint. Make sure MVMC machine has installed the management certificate and store in Personal Certificate folder. Use makecert to create a management certificate and upload to Azure.
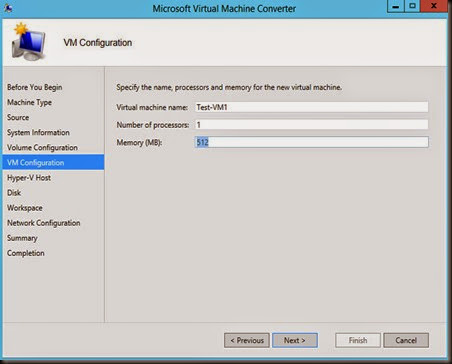
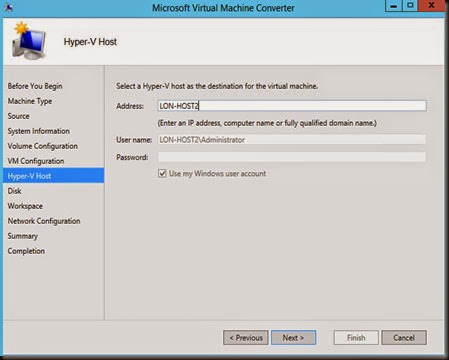
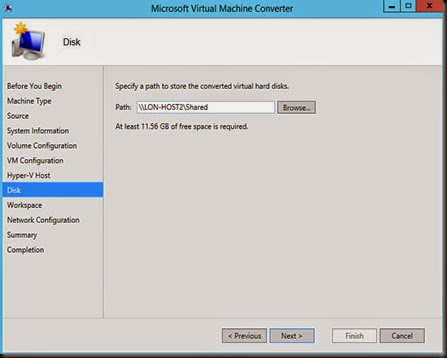
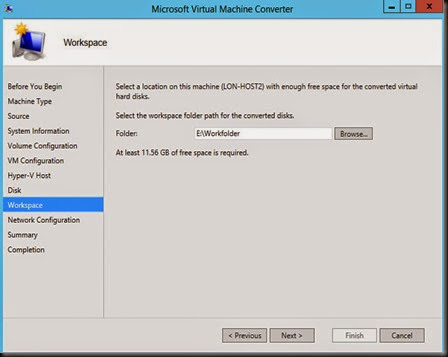
[ Configuration ]
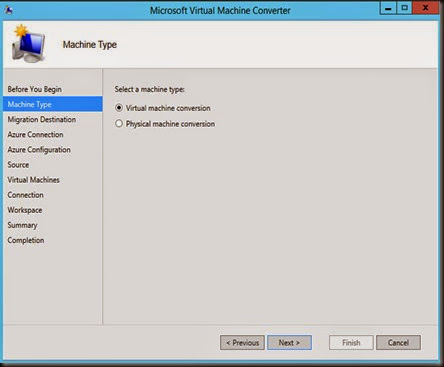
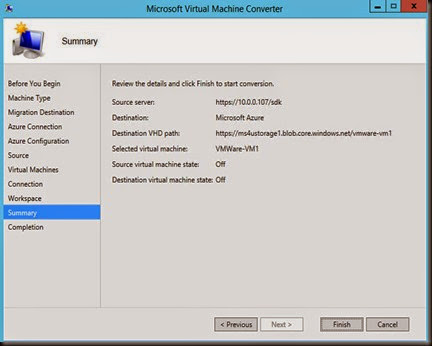
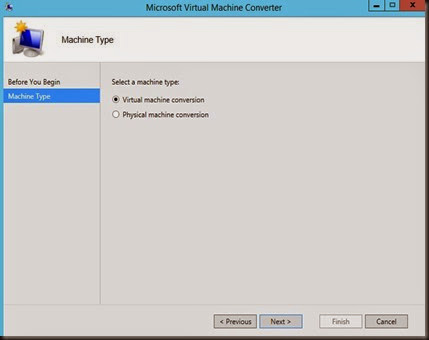
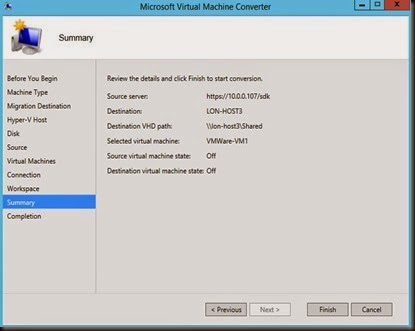
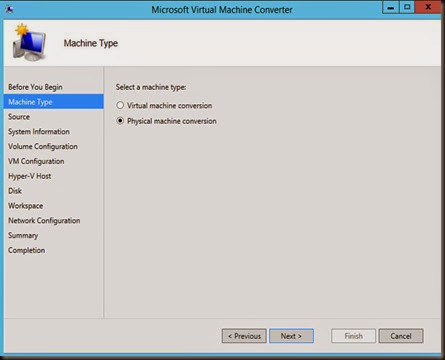
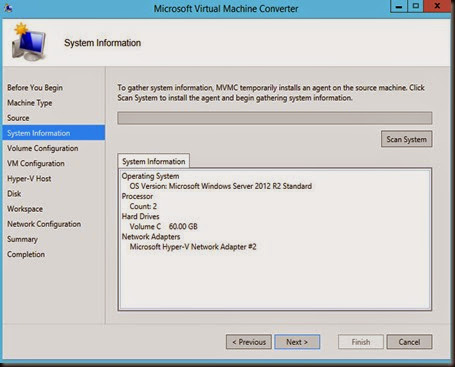
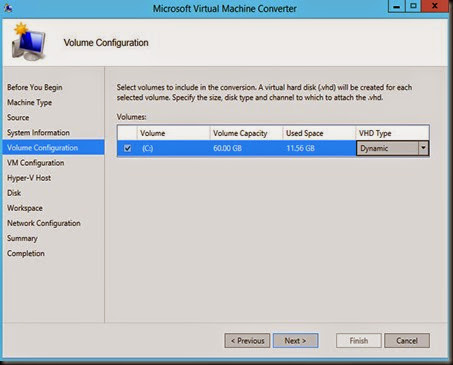
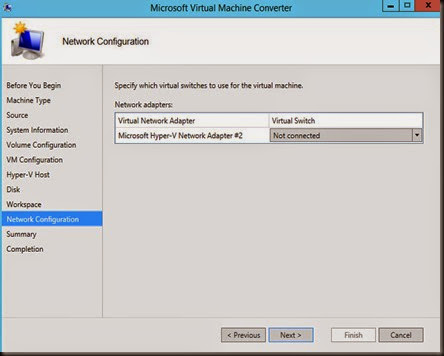
- Select virtual machine conversion. It will convert Vmware to VHD first.
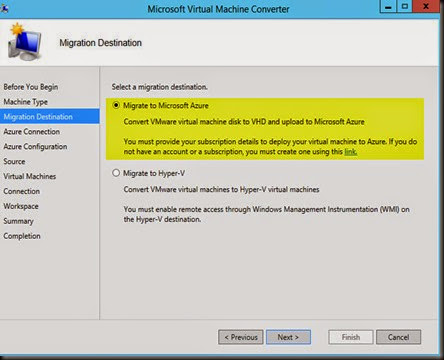
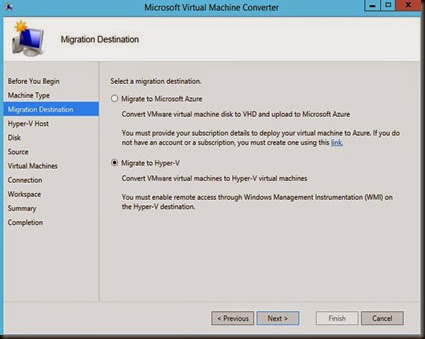
- Migrate to Microsoft Azure after conversion complete
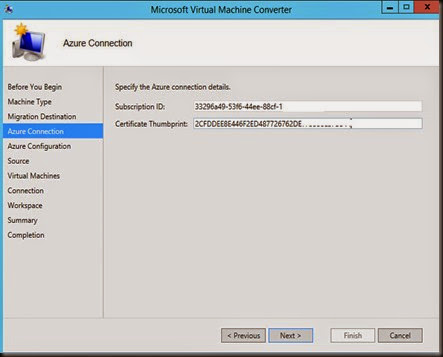
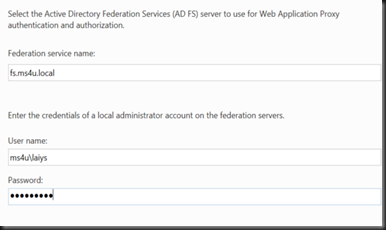
- Enter Azure subscription ID and certificate thumbprint
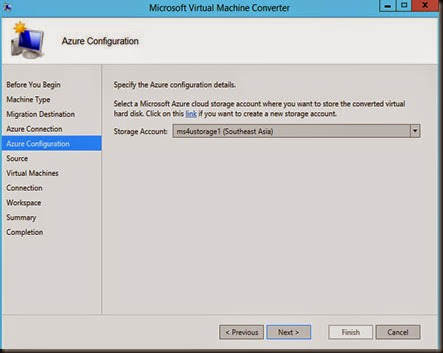
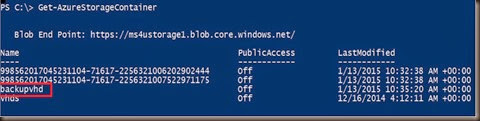
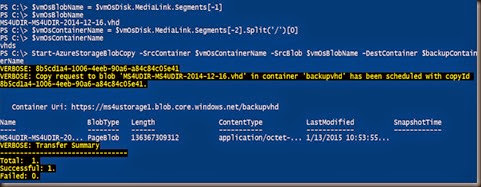
- Select destination Azure Storage to store VHD
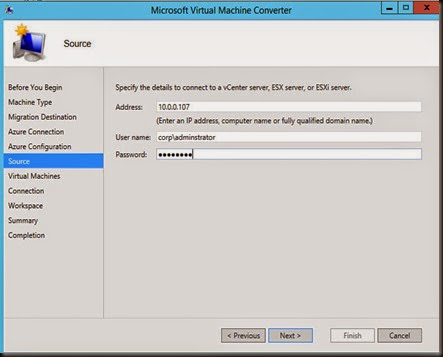
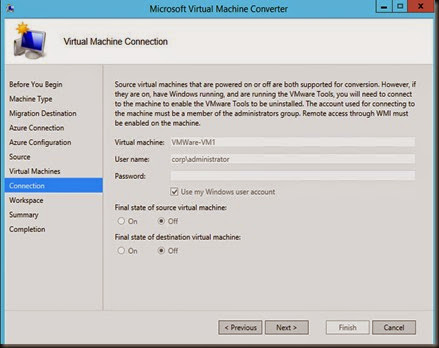
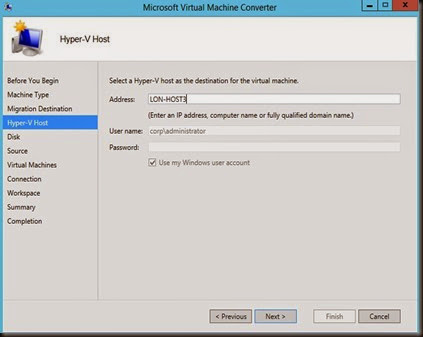
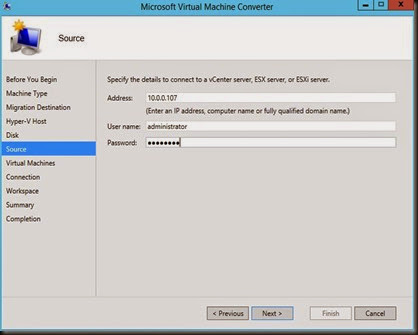
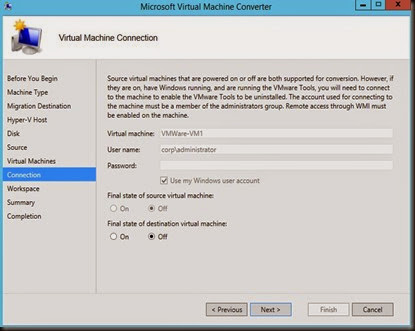
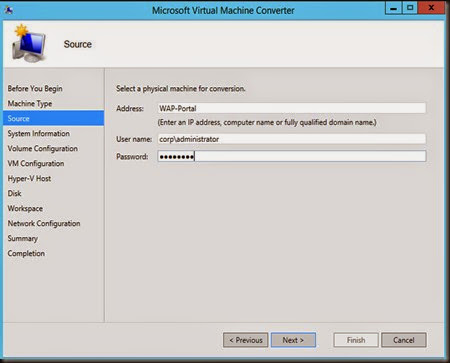
- Connect to Vmware Vcenter or ESX Host
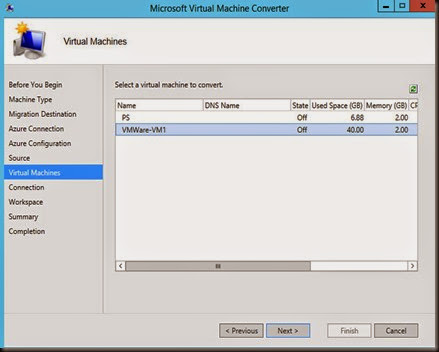
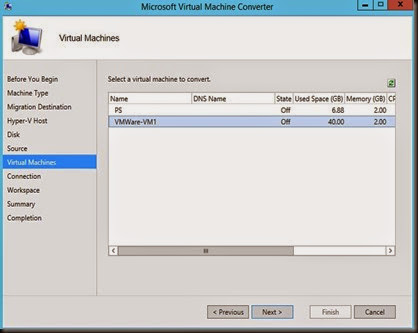
- Select Vmware VM
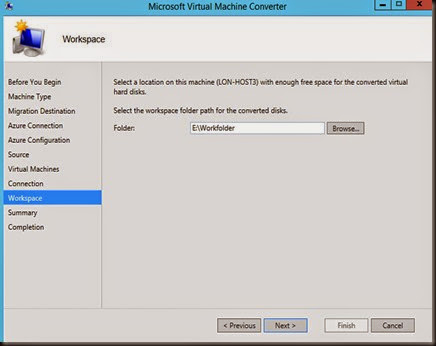
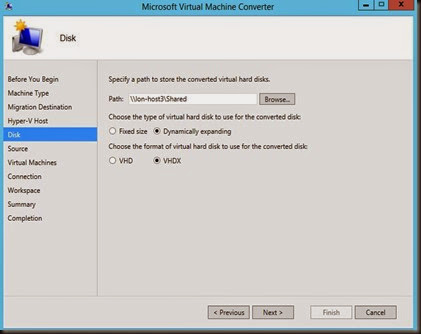
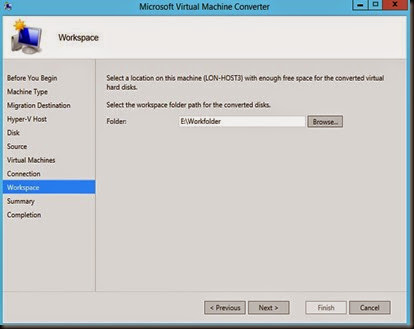
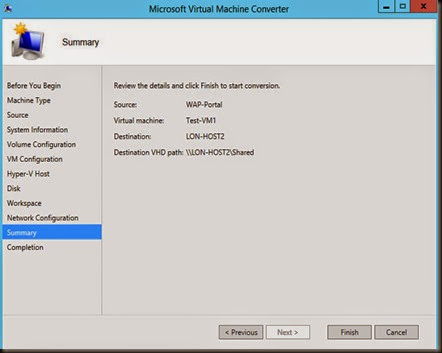
- Select temporary storage to hold the virtual disk during conversion and click Finish to start the conversion before upload to Azure
[ End result]
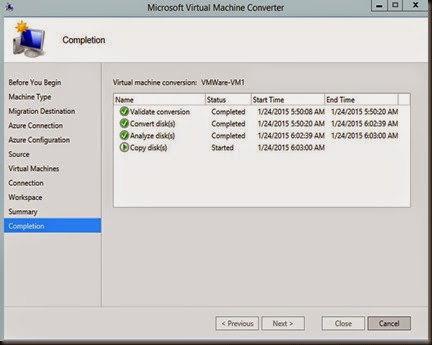
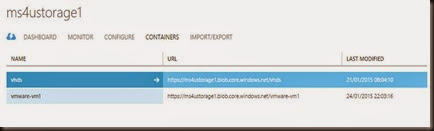
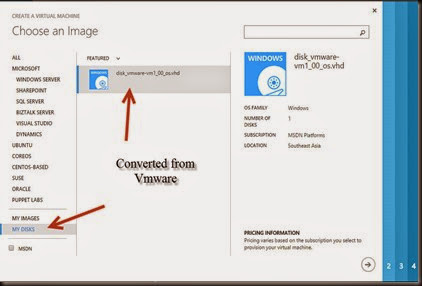
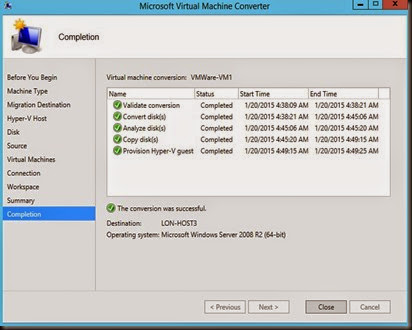
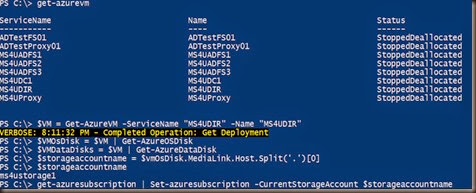
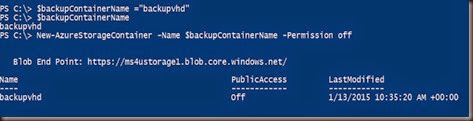
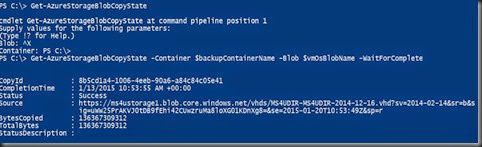
We leave the system run overnight. On the next day, we found that the vmware has completed the conversion and uploaded to Azure. Virtual disk has successful transfer to Azure Storage. Our next step is create a VM by clicking on + NEW | Compute | Virtual Machine | From Gallery |
Select MY DISK | Select your virtual disk and create your VM on Microsoft Azure
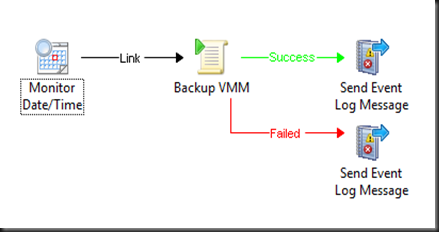
That’s all for now. We have just completed using MVMC 3.0 to
Migrate VMware to Azure. Feel free to check out other capabilities of MVMC 3.0: