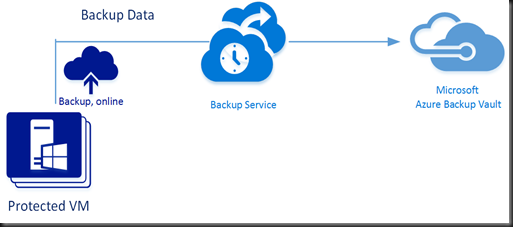
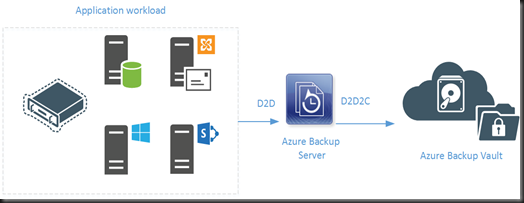
Recently Microsoft has enhanced Microsoft Azure Backup to protect on-premise application workload.
You can use it to backup
- SQL Server
- Hyper-V VM
- Sharepoint Server
- Microsoft Exchange
- Windows Client
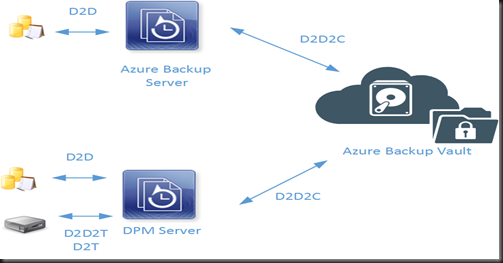
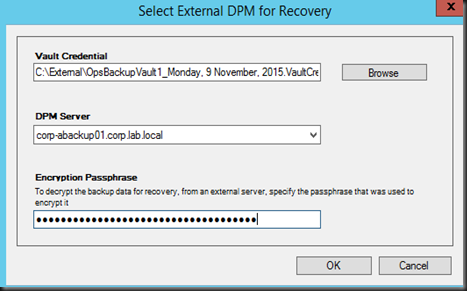
It can support
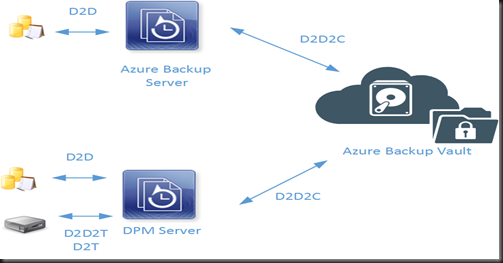
- Disk to Disk (short term)
- Disk to Disk to Cloud (long term)
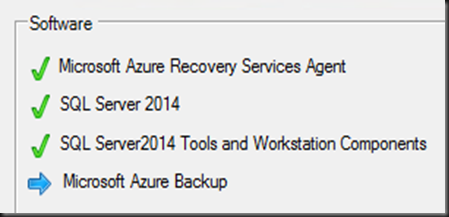
[ Installation ]
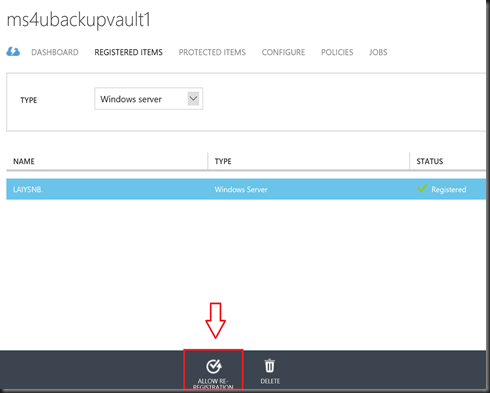
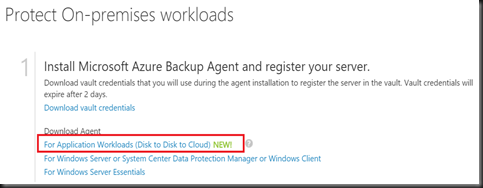
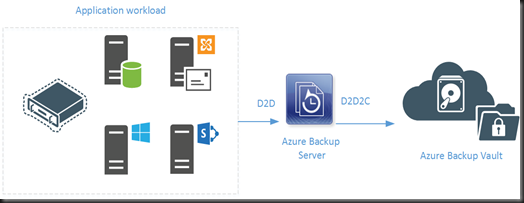
- Create Backup Vault
- Download Installer from Microsoft Azure Management Portal after create backup vault. Installer size around 3.17GB
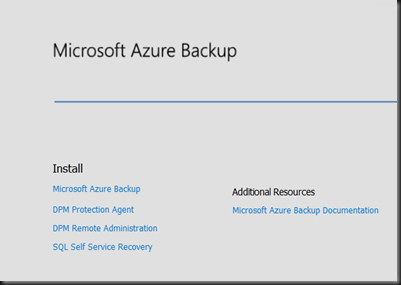
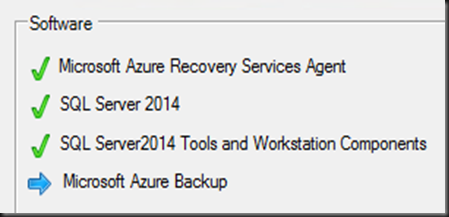
- Install on Window Server 2012 R2 Virtual Machine. During installation, we found out the the interface and installation similar like Microsoft System Center Data Protection Manager.
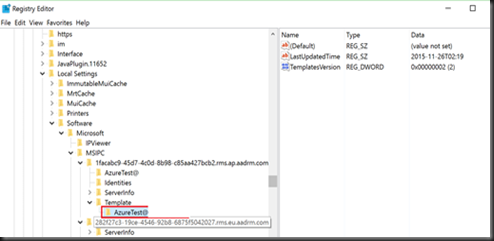
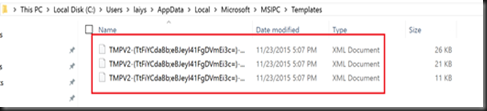
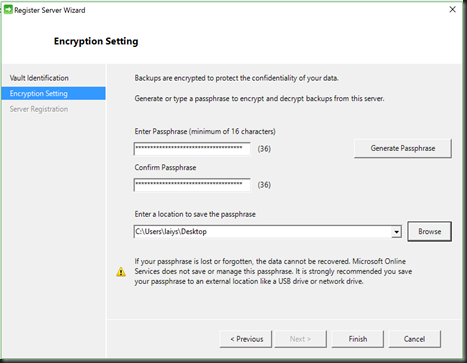
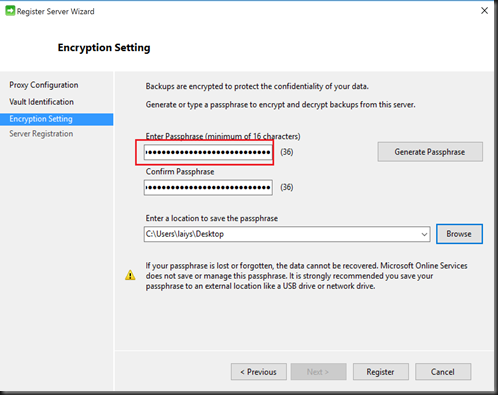
The system will ask for vault credential to register Azure Backup Vault during installation. For the remaining installation, do check out this post on the installation screenshot:- https://azure.microsoft.com/en-us/documentation/articles/backup-azure-microsoft-azure-backup/
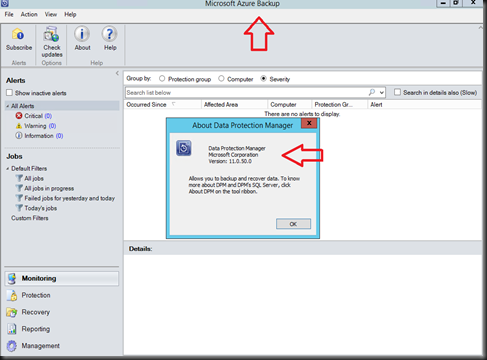
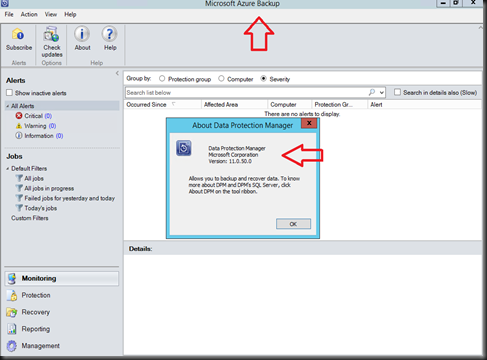
After installation, double click icon on desktop (Microsoft Azure Backup Server)

Gosh! It’s DPM Server but without tape support and integration with other System Center.
[ Configuration ]
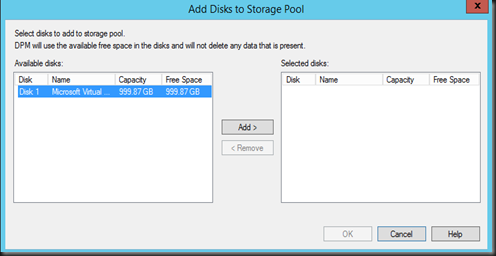
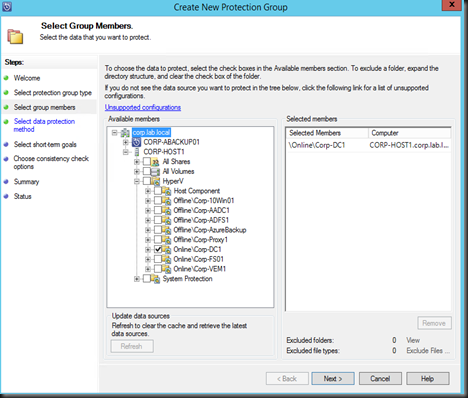
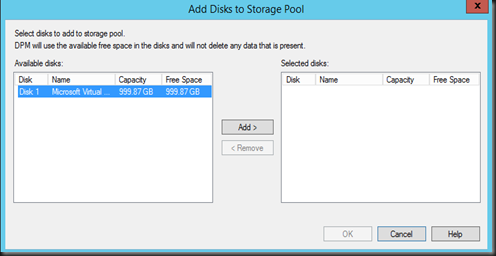
Before begin to protect workload, you’re require to
- add Disk Pool for D2D Backup
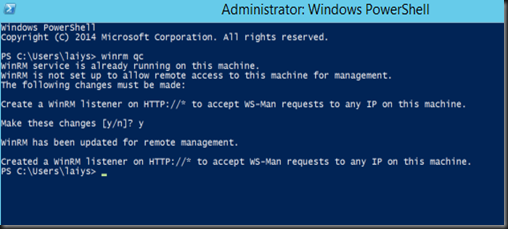
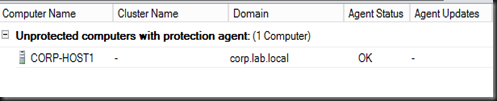
- Install Azure Backup Agent. You can install an agent if the workload has not install with DPM agent or Azure Backup agent.
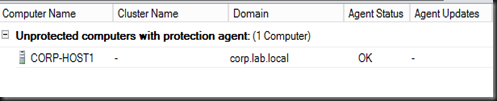
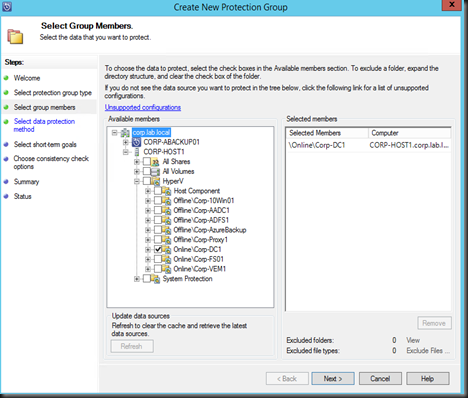
- Create Protection Group to start protect application workload
You can configure D2D or D2D2C. By using Azure Backup Server, you’ll be billing according to the following pricing:- https://azure.microsoft.com/en-us/pricing/details/backup/
You will still be billed per protected instance even D2D. Just that no charges on Azure storage as you’re using local disk.
To summarize, you need to pay per protected instance + storage consumed (when configure D2D2C)
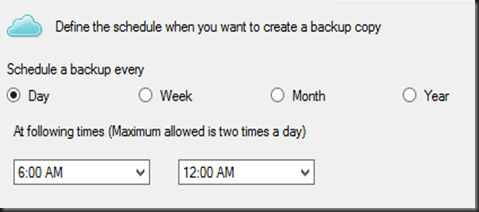
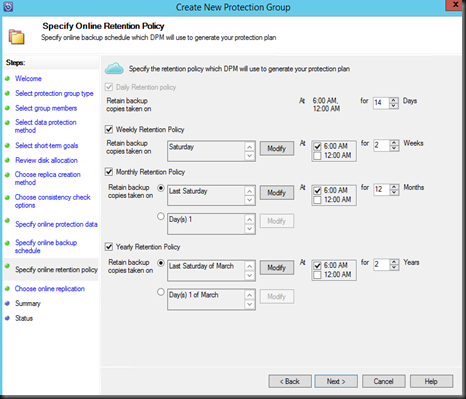
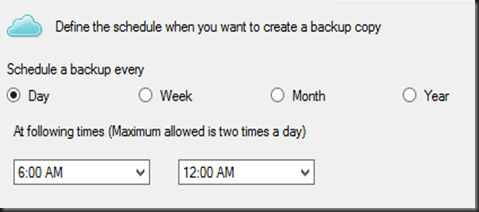
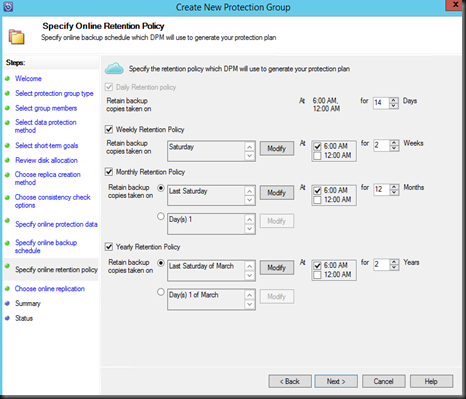
For Cloud backup, you can specify maximum of 2 backup time for daily backup.
You can set weekly, month and yearly retention range.
Make sure you have internet connection to Microsoft Azure. After 15 days without Internet connection, backup job will stop working but you can still restore from Azure and from disk.
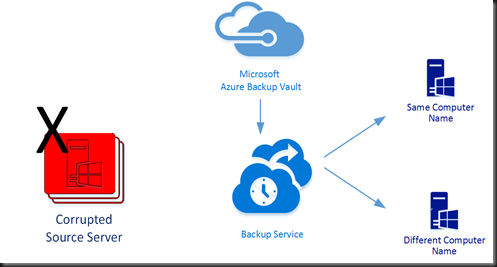
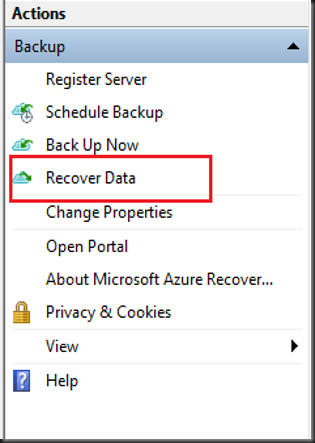
[Recovery]
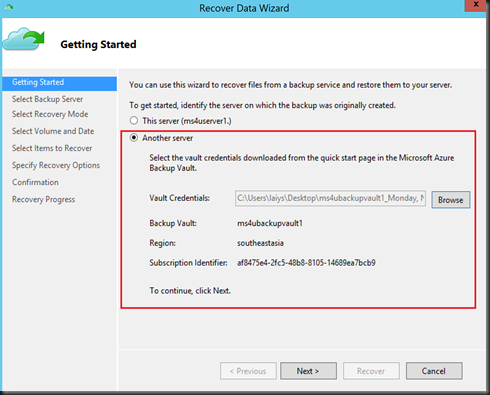
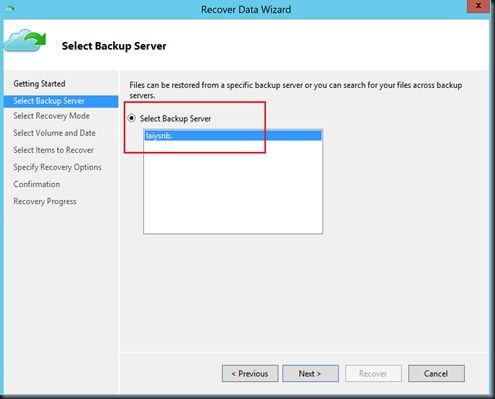
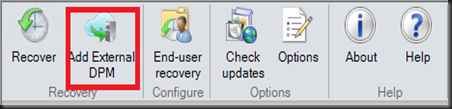
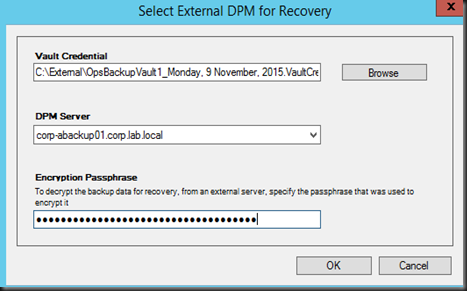
We found out that it also has an option to recovery from another DPM on backup vault.
Only DPM servers associated with the same registration vault can recover each other’s data.
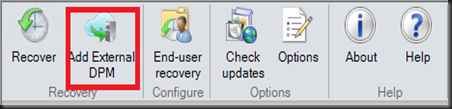
Add External DPM option is available after install with UR7 (for existing DPM Server) and latest Azure Backup Agent. You can now recover the data you've protected to an Azure Backup vault from any DPM server registered to that vault.
[ Summary ]
Azure Backup Server come handy when customer would like to protect the workload without require to buy System Center license but provide customer ability to backup to Azure. (Cloud).
In term of learning curve, configuration to protect and restore workload is similar like DPM configuration. Therefore, you would not have any difficulty if you have DPM knowledge.