[Updated – 13 August 2015]
We just deployed Microsoft Advanced Threat Analytics (ATA) into our environment to evaluate how powerful the product on automatically analyzing, learning and identifying normal and abnormal behavior. Its also help on identify known malicious attacks, security issues and risk using world class, cutting edge research in behavioral analytics to help enterprise identify security breaches before they cause damage.
ATA is now part of EMS products!
Version :- Preview Edition
Download ATA from - http://www.microsoft.com/en-us/server-cloud/enterprise-mobility/free-trial.aspx
Pricing:- From http://www.microsoft.com/en-us/server-cloud/enterprise-mobility/pricing.aspx

Screenshot taken on 5th August 2015. Subject to change.
[Setup]
- One virtual machine for ATA Center running Win 2012 R2 with latest Windows update
- One virtual machine for ATA Gateway running Win 2012 R2 with latest Windows update
- Domain controller running on Windows Server 2008 and later
Each ATA deployment can monitor one domain and up to 10 domain controllers depending on the network traffic to and from the domain controllers. During Preview version, one ATA only can monitor a domain. If you do have multiple domain, just deploy another ATA.
[ATA Center VM]
- Install ATA Center
- Login in to get ATA Gateway Setup software

[ ATA Center Gateway VM]
- Install ATA Center Gateway
- Configure static IP Address
- Configure DNS suffix with your own domain name (on Mgmt NIC)

- Configure 2 Interface : Management & Capture NIC
- Set IP
1.1.1.1/8without dns and gateway on Capture NIC

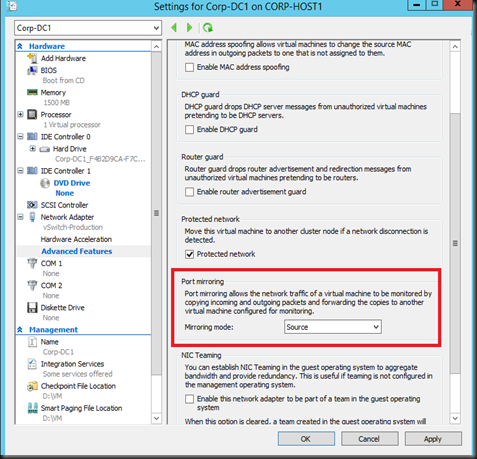
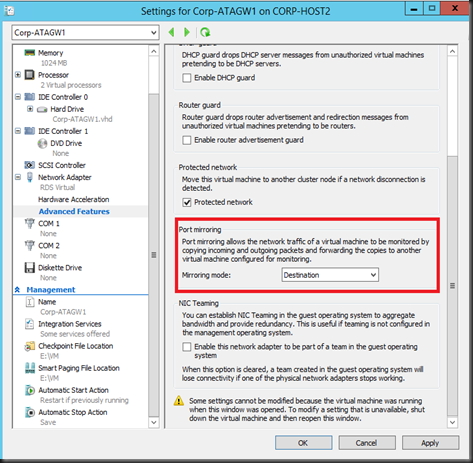
[ Configure Port Mirroring on Virtual Switch]
Configure Port mirroring. You can refer to our previous post.
Domain Controller VM – Set as Source on Port Mirroring
ATA Gateway VM – Set as Destination on Port Mirroring
[Updated –13 August 2015- Extra configuration]
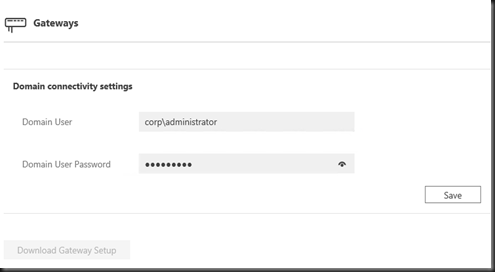
1. On Gateway, enter
- FQDN Domain Controller
- Select Capture Network Adapter
2. On Detection, enter
VPN subnet – 192.168.138.0/24 (your network)
Honeyaccount SID – (enter one of the domain user account SID)
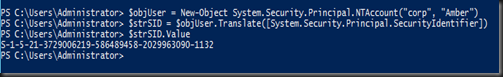
Our example:
- Useraccount- Amber
- Domain – corp
$objUser = New-Object System.Security.Principal.NTAccount("corp", "Amber") |

Do we have any suspicious activities? Well, no at this moment.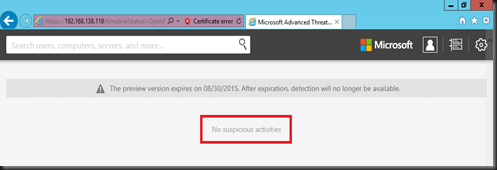
Bookmark this page!
We will update the result after 21 days starting from today. Why 21 days? Well, the ATA Center requires a minimum of 21 days of data for user behavioral analytics.
Stay Tuned!